Tag: linux
-
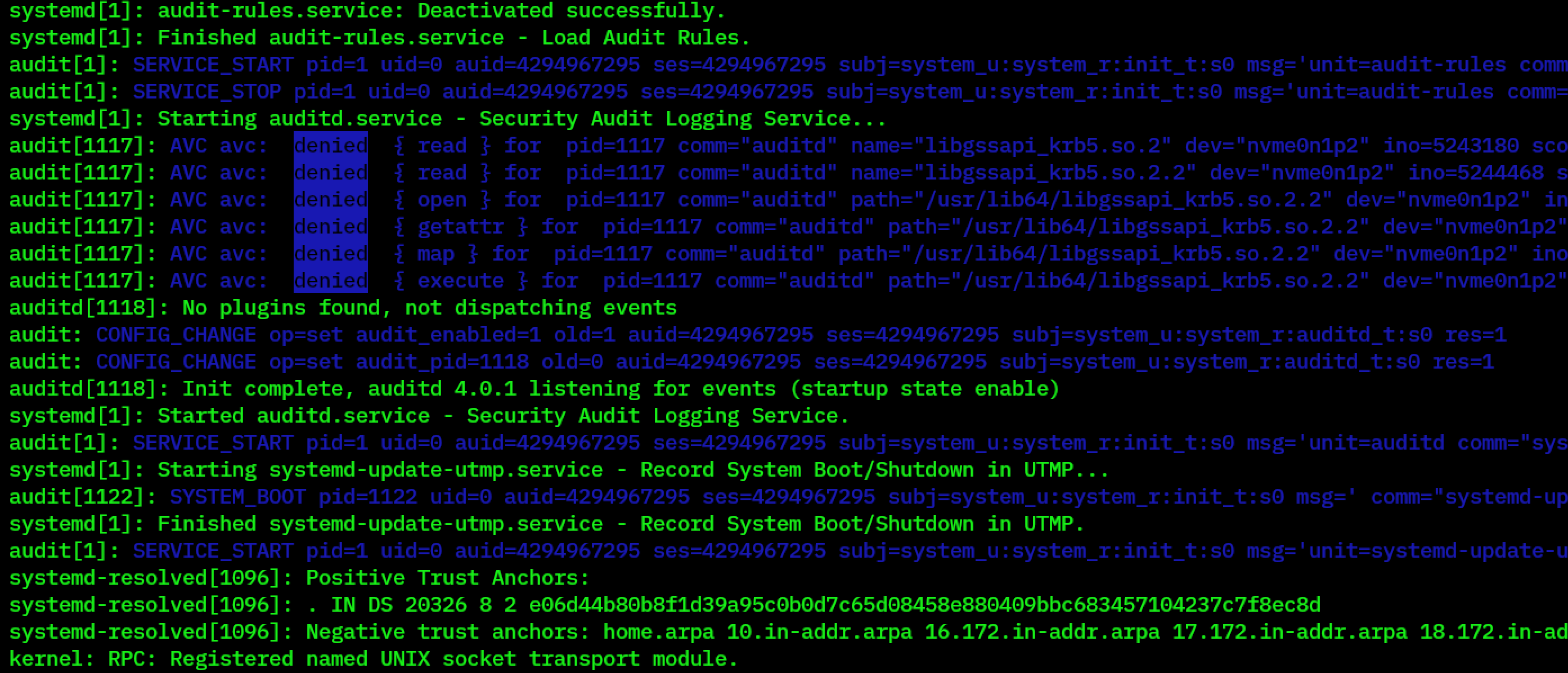
Fedora Core 40 and SELinux
Somehow, something broke my Linux desktop yesterday. Booted up early in the morning, everything worked fine. Downloaded some updates, browsed the web, and then rebooted. Post-reboot, all I got was a black screen when SDDM was meant to be executing. Fedora Core 40 locks the root account, which means the rescue option in GRUB doesn’t…
-
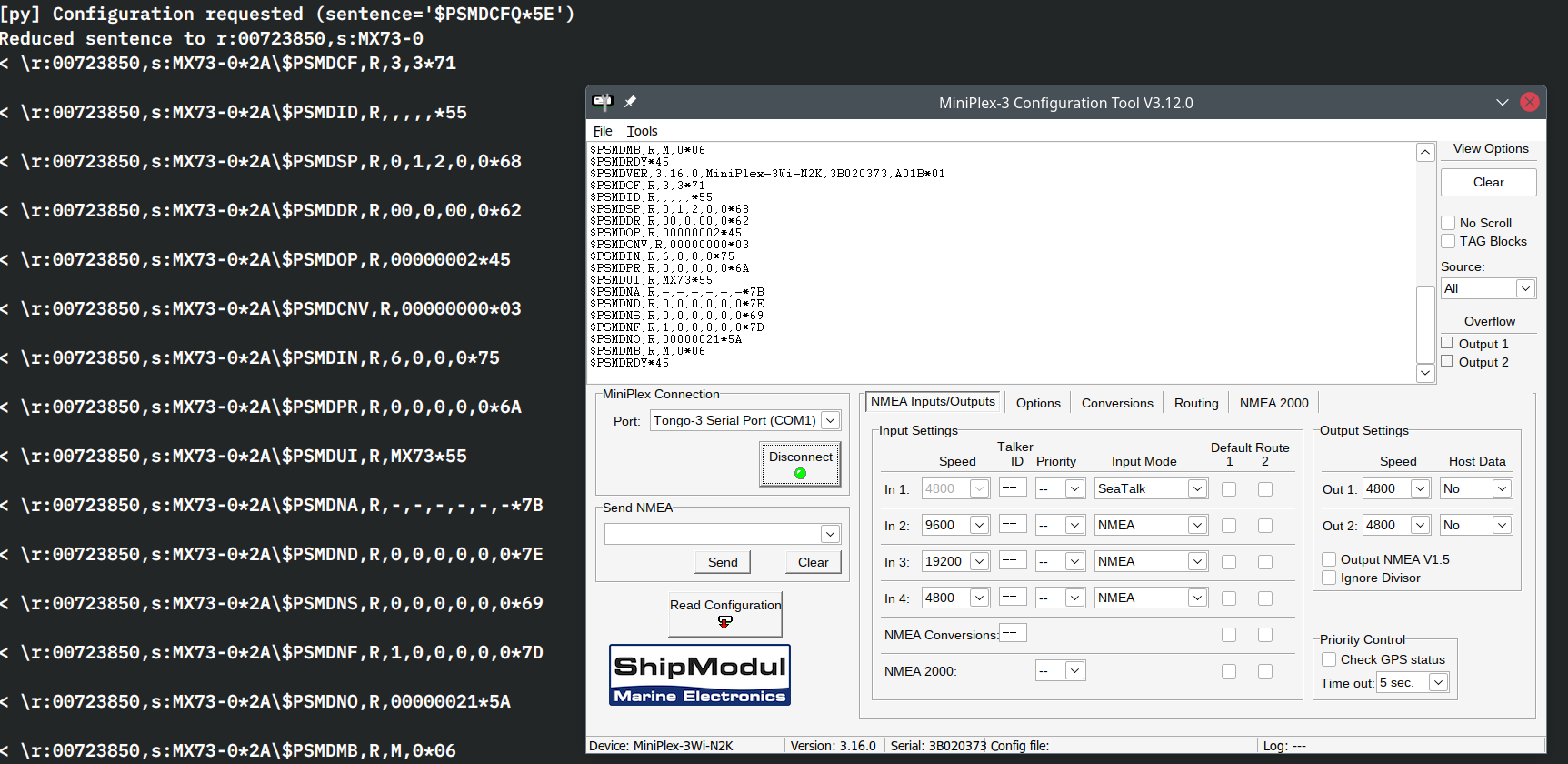
MiniPlex and Linux – the socat edition
Getting the Windows executable for the MiniPlex configuration program working was pretty neat. What would be neater is being able to perhaps write a Linux-native (or platform-agnostic) program that can at least display the configuration and stream the activity. Perhaps even update the configuration, though new versions of the firmware would result in new features…
-

Doubling up on 2FA
I haven’t used passwords to log in to my server for years; I’ve been using key-based authentication. This works pretty well, and I can even use 1Password’s integration as an SSH agent to hold the keys so that wherever I go, the keys are available to me. As a “learn how to do it”, I’ve…
-
LXD, dnsmasq, IPv6 reverse lookups
My residential ISP doesn’t offer reverse lookups for their IPv6 blocks that they delegate out with the PD flag to consumer routers. This causes some annoying slow-downs when talking to the various services I’m running in LXD containers, since a lot of them do reverse DNS lookups. Under the hood, LXD relies on dnsmasq to…
-
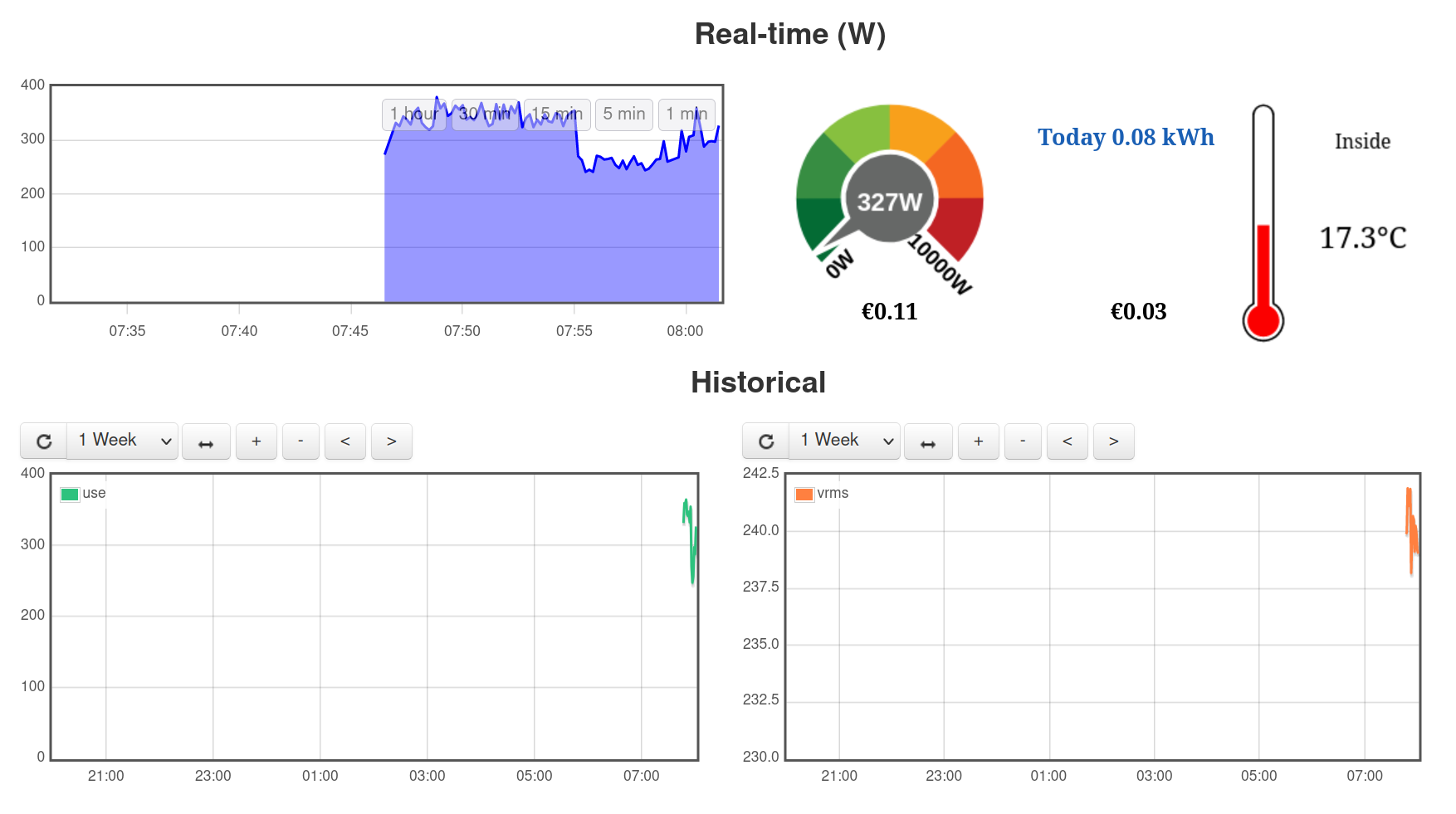
Running emoncms in a Linux container
When I was renovating the house I currently live in, I picked up an EmonTx v3 and some clip-on current sensors from OpenEnergyMonitor.org so that I could monitor the house power consumption more accurately than just getting a bill every 2 months from my energy supplier (even with a smart meter installed, they only provide…
-
Rebuilding Cricalix.Net – Part 4
While on holiday, I read a forum post that mentioned a “new” web server called Caddy. I took a look at it, and was intrigued by the integrated TLS certificate renewal using Let’s Encrypt. With NGINX or Apache, I have to run Certbot or similar to maintain the certificates, and I have to deal with…